By: Ali Elizabeth Turner
By: Ali Elizabeth Turner
I grew up knowing about Mata Hari and Tokyo Rose, and had only a cursory understanding of what has come to be known in espionage as the “honeytrap,” i.e., the flagrant, proactive use of the power of a woman’s sexuality to secure intel. Sometimes, the strategy is known as “pillow talk,” but it all comes back to the same premise: if you want to get state secrets, the best ones are typically divulged in compromising circumstances. Just ask Congressman Eric Swalwell, who amazingly is still on the House Intelligence Committee after having a dubious relationship with a female Chinese spy! And, the great irony is that her name is, wait for it…“Fang!”
Recently, the IDF (Israeli Defense Force) was targeted by Hamas militants who were posing online as beautiful Israeli women. The soldiers were encouraged to communicate on various social media platforms, never knowing that they were downloading malware which was embedded in fake photo-sharing apps.

Lieutenant Colonel Jonathan Conricus, an IDF Army spokesman, said they have successfully thwarted the cyberattack, which is the third such attempt over the last three-and-a-half years. He also described it as being “more advanced and sophisticated than the previous attempts.”
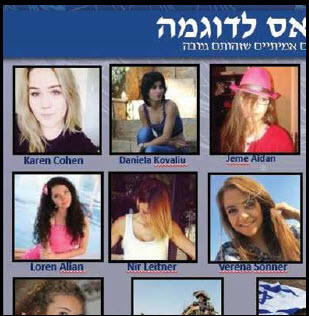
The new strategy was to have the “women” claim that they had hearing difficulties and could not speak on the phone. The communiques did successfully use Israeli slang, doctored photos, managed to block attempts to do reverse online searches, and sent generic voice messages in order to increase credibility. Some of the “names” of the faux honeys were Karen Cohen, Daniela Kovaliu, Jeme Aidan, Loren Alian, Nir Leitner, and Verena Sonner; and it is not known yet how many IDF soldiers were approached.
The downloaded malware made it possible for Hamas to control the individual IDF soldiers’ phones, transfer files, lift phone data, read messages, and use cameras to remotely take pictures. Conricus said that Hamas has been upping their game, but was glad that the IDF was able to thwart the attack.
Later on, the IDF tweeted, “What Hamas didn’t know was that Israeli intelligence caught onto their plot, tracked the malware, and downed Hamas’ hacking system.”
If the classic honeypot approach didn’t work, then encouraging the soldiers to download fake insider access to the World Cup tried to. I guess if you can’t get a guy to “kick it” one way, you’ll try to get him to “kick it” another. I am sure that the IDF soldiers that got tricked by one of the world’s oldest strategies have had to eat a lifetime supply of industrial-strength humble pie, and I can’t imagine the day of reckoning they endured.
I would assume that because Israel is our strongest ally, they have shared with “our guys” what went down and how Hamas was able to do what they did. I would also guess that they have put their heads together to make sure that both of our countries are stronger by being more secure against the misuse of that which was always designed to be sacred. One can only hope.
By: Ali Elizabeth Turner